The little-known Japanese company at the center of a legal tussle between Apple Inc. and the U.S. government over the hacking of an iPhone built its business on pinball game machines and stumbled into the mobile phone security business almost by accident.
Cellebrite Mobile Synchronization Ltd. worked with the FBI to crack an iPhone connected in a terrorist attack, according to people familiar with the matter, who asked not to be identified as the matter is private. Neither Cellebrite nor the FBI have confirmed the link, and a spokesman from parent Sun Corp. on Thursday said the company isn’t able to comment on specific criminal cases.
Sun, based in a small town of 100,000 southwest of Tokyo, has been building pinball-like game machines found in Japan’s pachinko parlors since the 1970s but has often displayed bigger tech ambitions. The Konan, Aichi-based company developed personal computers in the late 1970s, computer games and more recently, iPhone mahjong apps. In 2007, as sales slumped, Sun acquired Petah Tikva, Israel-based Cellebrite.
Cellebrite hadn’t ventured into forensics at the time, and the purchase was mainly to add phone-to-phone data transfer to Sun’s fledgling telecommunications business, said the Japanese company’s spokesman Hidefumi Sugaya. When Cellebrite later took on investigative agencies such as the Federal Bureau of Investigation as clients, the business took off, he said in a telephone interview. Today, the bulk of Sun’s mobile data solutions business comes from Cellebrite, said Sugaya.
Sun’s shares have surged since March 21, when U.S. authorities said a third party demonstrated a way to access data on the iPhone used in the San Bernardino, California, mass shooting last year. The shares rose 7 percent to 1,091 yen by the close of trading in Tokyo on Thursday.
“If it’s Cellebrite it’s probably good publicity for them,” said Bryce Boland, chief technology officer for Asia Pacific at security company FireEye Inc. “There are other companies as well that provide tools in this space, and Cellebrite are one of the best companies in this space.”
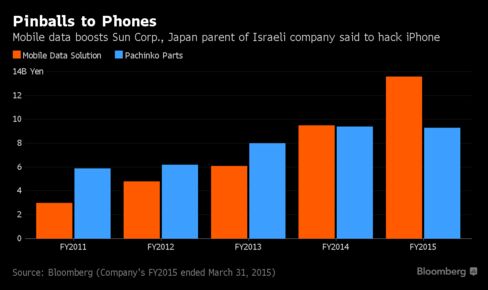
Revenue from Cellebrite’s mobile data solutions division overtook pachinko parts in Sun’s fiscal year ended March 2014 and contributed 13.6 billion yen ($121 million) or 50 percent of sales in the last fiscal year, according to data compiled by Bloomberg. It’s now the largest business segment for Sun.
Israeli daily Yedioth Ahronoth last week identified Cellebrite, which has captured a large slice of the mobile forensics market over the past decade, as the FBI’s partner in cracking the iPhone.

The U.S. Justice Department said on Tuesday it has gained access to the data on the shooter’s phone with third party help, and dropped its legal case against Cupertino, California-based Apple.
"Although the FBI didn’t get a legal decision that would require Apple to hack around its own security software, it created a situation where they can go to third parties to do that," said Matt Larson, an analyst at Bloomberg Intelligence. "Companies like Cellebrite may have found a niche industry of assisting the FBI unlock personal devices in select cases moving forward."
Cellebrite sells hardware and software for extracting data from hand-held devices, even if it has been encrypted or deleted. It employs more than 500 people and has offices in Israel, the U.S., Brazil, Germany, Singapore and the U.K., according to its website. Founded in 1999, Cellebrite was bought by Sun Corp. for a reported $17.5 million.
The value of forensics companies such as Cellebrite, particularly for law enforcement agencies, goes beyond accessing encrypted data, according to Jonathan Zdziarski, a cyber-security researcher and iPhone security expert who consults with law enforcement.
Study Patches
"As you copy the evidence from the phone, you need to be able to catalog it and demonstrate you haven’t tampered with it -- show that the file that came from the phone is the same file you are using in court," he said. "There have been plenty of free hacking tools available -- it’s not just about getting to the data. All of these problems are addressed by forensics companies like Cellebrite."
The Israeli firm may have been able to come up with a method to crack the iPhone from studying patches that Apple’s released, or updates to software that fix vulnerabilities, said FireEye’s Boland, adding he had no direct knowledge of this case.
“It’s a fairly straightforward method for a researcher to identify what has been changed, and from that reverse-engineer what the flaw was and then build a tool to exploit that flaw,” he said.

No comments:
Post a Comment